UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
WASHINGTON, D.C. 20549
FORM 10-Q
x | QUARTERLY REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 |
For the quarterly period ended March 31, 2014
Commission file number: 001-35671
LifeLock, Inc.
(Exact name of registrant as specified in its charter)
Delaware |
|
56-2508977 |
(State or other jurisdiction of incorporation or organization) |
|
(I.R.S. Employer Identification No.) |
60 East Rio Salado Parkway, Suite 400
Tempe, Arizona 85281
(Address of principal executive offices and zip code)
(480) 682-5100
(Registrant’s telephone number, including area code)
Indicate by check mark whether the registrant: (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities Exchange Act of 1934 during the preceding 12 months (or for such shorter period that the registrant was required to file such reports), and (2) has been subject to such filing requirements for the past 90 days. Yes x No ¨
Indicate by check mark whether the registrant has submitted electronically and posted on its corporate Web site, if any, every Interactive Data File required to be submitted and posted pursuant to Rule 405 of Regulation S-T (§232.405 of this chapter) during the preceding 12 months (or for such shorter period that the registrant was required to submit and post such files). Yes x No ¨
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, or a smaller reporting company. See the definitions of “large accelerated filer,” “accelerated filer” and “smaller reporting company” in Rule 12b-2 of the Exchange Act. (Check one):
Large accelerated filer |
x |
Accelerated filer |
¨ |
|
|
|
|
Non-accelerated filer |
¨ (Do not check if a smaller reporting company) |
Smaller reporting company |
¨ |
Indicate by check mark whether the registrant is a shell company (as defined in Rule 12b-2 of the Exchange Act). Yes ¨ No x
As of April 25, 2014, there were outstanding 92,399,121 shares of the registrant’s common stock, $0.001 par value.
LIFELOCK, INC.
QUARTERLY REPORT ON FORM 10-Q
FOR THE QUARTER ENDED MARCH 31, 2014
TABLE OF CONTENTS
|
|
Page |
|
|
|
|
|
|
|
|
|
|
1 |
|
|
|
1 |
|
|
|
|
2 |
|
|
|
|
|
3 |
|
|
|
|
|
4 |
|
|
|
|
|
5 |
|
|
|
|
Item 2. Management’s Discussion and Analysis of Financial Condition and Results of Operations |
|
12 |
|
|
|
Item 3. Quantitative and Qualitative Disclosures About Market Risk |
|
27 |
|
|
|
|
27 |
|
|
|
|
|
|
|
|
|
|
|
28 |
|
|
|
|
|
28 |
|
|
|
|
|
29 |
|
|
|
|
|
30 |
i
PART I – FINANCIAL INFORMATION
Item 1. Financial Statements (Unaudited)
LIFELOCK, INC.
CONDENSED CONSOLIDATED BALANCE SHEETS
(in thousands, except share data)
(unaudited)
|
March 31, 2014 |
|
|
December 31, 2013 |
|
||
Assets |
|
|
|
|
|
|
|
Current assets: |
|
|
|
|
|
|
|
Cash and cash equivalents |
$ |
143,702 |
|
|
$ |
123,911 |
|
Marketable securities |
|
47,522 |
|
|
|
48,688 |
|
Trade and other receivables, net |
|
10,601 |
|
|
|
10,906 |
|
Deferred tax assets, net |
|
16,668 |
|
|
|
13,117 |
|
Prepaid expenses and other current assets |
|
9,777 |
|
|
|
6,961 |
|
Total current assets |
|
228,270 |
|
|
|
203,583 |
|
Property and equipment, net |
|
18,064 |
|
|
|
16,504 |
|
Goodwill |
|
158,152 |
|
|
|
158,152 |
|
Intangible assets, net |
|
44,982 |
|
|
|
47,213 |
|
Deferred tax assets, net – noncurrent |
|
35,986 |
|
|
|
35,986 |
|
Other noncurrent assets |
|
1,561 |
|
|
|
1,812 |
|
Total assets |
$ |
487,015 |
|
|
$ |
463,250 |
|
Liabilities and stockholders’ equity |
|
|
|
|
|
|
|
Current liabilities: |
|
|
|
|
|
|
|
Accounts payable |
$ |
4,493 |
|
|
$ |
2,422 |
|
Accrued expenses and other liabilities |
|
34,067 |
|
|
|
34,926 |
|
Deferred revenue |
|
136,319 |
|
|
|
119,106 |
|
Total current liabilities |
|
174,879 |
|
|
|
156,454 |
|
Other noncurrent liabilities |
|
5,411 |
|
|
|
4,640 |
|
Total liabilities |
|
180,290 |
|
|
|
161,094 |
|
Commitments and contingencies |
|
|
|
|
|
|
|
Stockholders’ equity: |
|
|
|
|
|
|
|
Common stock, $0.001 par value, 300,000,000 authorized at March 31, 2014 and December 31, 2013; 92,326,684 and 91,441,771 shares issued and outstanding at March 31, 2014 and December 31, 2013, respectively |
|
92 |
|
|
|
91 |
|
Preferred stock, $0.001 par value, 10,000,000 shares authorized and no shares issued and outstanding at March 31, 2014 and December 31, 2013, respectively |
|
- |
|
|
|
- |
|
Additional paid-in capital |
|
479,365 |
|
|
|
469,636 |
|
Accumulated other comprehensive loss |
|
(10 |
) |
|
|
(18 |
) |
Accumulated deficit |
|
(172,722 |
) |
|
|
(167,553 |
) |
Total stockholders’ equity |
|
306,725 |
|
|
|
302,156 |
|
Total liabilities and stockholders’ equity |
$ |
487,015 |
|
|
$ |
463,250 |
|
See accompanying notes to condensed consolidated financial statements.
1
LIFELOCK, INC.
CONDENSED CONSOLIDATED STATEMENTS OF OPERATIONS
(in thousands, except per share amounts)
(unaudited)
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
Revenue: |
|
|
|
|
|
|
|
Consumer revenue |
$ |
100,995 |
|
|
$ |
75,094 |
|
Enterprise revenue |
|
6,591 |
|
|
|
7,001 |
|
Total revenue |
|
107,586 |
|
|
|
82,095 |
|
Cost of services |
|
30,067 |
|
|
|
23,804 |
|
Gross profit |
|
77,519 |
|
|
|
58,291 |
|
Costs and expenses: |
|
|
|
|
|
|
|
Sales and marketing |
|
56,847 |
|
|
|
41,793 |
|
Technology and development |
|
13,148 |
|
|
|
9,024 |
|
General and administrative |
|
13,972 |
|
|
|
9,424 |
|
Amortization of acquired intangible assets |
|
2,231 |
|
|
|
1,966 |
|
Total costs and expenses |
|
86,198 |
|
|
|
62,207 |
|
Loss from operations |
|
(8,679 |
) |
|
|
(3,916 |
) |
Other income (expense): |
|
|
|
|
|
|
|
Interest expense |
|
(87 |
) |
|
|
(67 |
) |
Interest income |
|
60 |
|
|
|
20 |
|
Other |
|
(11 |
) |
|
|
(4 |
) |
Total other expense |
|
(38 |
) |
|
|
(51 |
) |
Loss before provision for income taxes |
|
(8,717 |
) |
|
|
(3,967 |
) |
Income tax (benefit) expense |
|
(3,548 |
) |
|
|
150 |
|
Net loss |
$ |
(5,169 |
) |
|
$ |
(4,117 |
) |
Net loss attributable per share to common stockholders: |
|
|
|
|
|
|
|
Basic |
$ |
(0.06 |
) |
|
$ |
(0.05 |
) |
Diluted |
$ |
(0.06 |
) |
|
$ |
(0.05 |
) |
Weighted-average common shares outstanding: |
|
|
|
|
|
|
|
Basic |
|
91,903 |
|
|
|
86,640 |
|
Diluted |
|
91,903 |
|
|
|
86,640 |
|
See accompanying notes to condensed consolidated financial statements.
2
LIFELOCK, INC.
CONDENSED CONSOLIDATED STATEMENTS OF COMPREHENSIVE LOSS
(in thousands)
(unaudited)
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
Net loss |
$ |
(5,169 |
) |
|
$ |
(4,117 |
) |
Other comprehensive gain, net of tax: |
|
|
|
|
|
|
|
Unrealized gain on marketable securities |
|
8 |
|
|
|
- |
|
Comprehensive loss |
$ |
(5,161 |
) |
|
$ |
(4,117 |
) |
|
|
|
|
|
|
|
|
See accompanying notes to condensed consolidated financial statements.
3
LIFELOCK, INC.
CONDENSED CONSOLIDATED STATEMENTS OF CASH FLOWS
(in thousands)
(unaudited)
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
Operating activities |
|
|
|
|
|
|
|
Net loss |
$ |
(5,169 |
) |
|
$ |
(4,117 |
) |
Adjustment to reconcile net loss to net cash provided by operating activities: |
|
|
|
|
|
|
|
Depreciation and amortization |
|
3,861 |
|
|
|
3,071 |
|
Share-based compensation |
|
5,475 |
|
|
|
2,724 |
|
Provision for doubtful accounts |
|
272 |
|
|
|
43 |
|
Accretion of marketable securities |
|
366 |
|
|
|
- |
|
Deferred income tax benefit |
|
(3,551 |
) |
|
|
- |
|
Other |
|
7 |
|
|
|
4 |
|
Change in operating assets and liabilities: |
|
|
|
|
|
|
|
Trade and other receivables |
|
(305 |
) |
|
|
(239 |
) |
Prepaid expenses and other current assets |
|
(2,816 |
) |
|
|
(2,720 |
) |
Other non-current assets |
|
251 |
|
|
|
313 |
|
Accounts payable |
|
2,776 |
|
|
|
225 |
|
Accrued expenses and other liabilities |
|
(835 |
) |
|
|
1,048 |
|
Deferred revenue |
|
17,213 |
|
|
|
12,477 |
|
Other non-current liabilities |
|
771 |
|
|
|
(34 |
) |
Net cash provided by operating activities |
|
18,316 |
|
|
|
12,795 |
|
Investing activities |
|
|
|
|
|
|
|
Acquisition of property and equipment |
|
(3,927 |
) |
|
|
(1,285 |
) |
Purchase of marketable securities |
|
(5,797 |
) |
|
|
- |
|
Sale and maturities of marketable securities |
|
6,921 |
|
|
|
- |
|
Net cash used in investing activities |
|
(2,803 |
) |
|
|
(1,285 |
) |
Financing activities |
|
|
|
|
|
|
|
Proceeds from: |
|
|
|
|
|
|
|
Stock based compensation plans |
|
4,432 |
|
|
|
36 |
|
Payments for: |
|
|
|
|
|
|
|
Employee tax withholdings related to restricted stock units |
|
(154 |
) |
|
|
- |
|
Debt issuance costs |
|
- |
|
|
|
(440 |
) |
Net cash provided by (used in) financing activities |
|
4,278 |
|
|
|
(404 |
) |
Net increase in cash and cash equivalents |
|
19,791 |
|
|
|
11,106 |
|
Cash and cash equivalents at beginning of period |
|
123,911 |
|
|
|
134,197 |
|
Cash and cash equivalents at end of period |
$ |
143,702 |
|
|
$ |
145,303 |
|
See accompanying notes to condensed consolidated financial statements.
4
LIFELOCK, INC.
NOTES TO CONDENSED CONSOLIDATED FINANCIAL STATEMENTS
(in thousands, except share and per share data)
(unaudited)
1. Description of Business and Basis of Presentation
We provide proactive identity theft protection services to our consumer subscribers, whom we refer to as our members, on an annual or monthly subscription basis. We also provide fraud and risk solutions to our enterprise customers.
We were incorporated in Delaware on April 12, 2005 and are headquartered in Tempe, Arizona. On March 14, 2012, we acquired ID Analytics, Inc. and its wholly-owned subsidiary IDA, Inc., collectively, ID Analytics, each of which is incorporated in Delaware. On December 11, 2013, we acquired Lemon, Inc., or Lemon, which is incorporated in Delaware.
Basis of Presentation
The accompanying unaudited condensed consolidated financial statements have been prepared in accordance with generally accepted accounting principles in the United States, or U.S. GAAP, and applicable rules and regulations of the Securities and Exchange Commission, or SEC, regarding interim financial reporting. Certain information and note disclosures normally included in financial statements prepared in accordance with U.S. GAAP have been condensed or omitted pursuant to such rules and regulations. Therefore, these condensed consolidated financial statements should be read in conjunction with the consolidated financial statements and notes included in our Annual Report on Form 10-K for the fiscal year ended December 31, 2013.
The condensed consolidated balance sheet as of December 31, 2013 included herein was derived from the audited financial statements as of that date, but does not include all disclosures including notes required by U.S. GAAP.
The accompanying unaudited condensed consolidated financial statements reflect all normal recurring adjustments necessary to present fairly the financial position, results of operations, and cash flows for the interim periods, but are not necessarily indicative of the result of operations to be anticipated for the entire year ending December 31, 2014 or any future period.
Basis of Consolidation
The condensed consolidated financial statements include our accounts and those of our wholly-owned subsidiaries. We eliminate all intercompany balances and transactions, including intercompany profits, and unrealized gains and losses in consolidation.
Use of Estimates
The preparation of condensed consolidated financial statements in conformity with U.S. GAAP requires us to make certain estimates and assumptions that affect the amounts reported in the condensed consolidated financial statements and accompanying notes. We base our estimates on historical experience, current business factors, and various other assumptions that we believe are necessary to consider in forming a basis for making judgments about the carrying values of assets and liabilities, the recorded amounts of revenue and expenses, and the disclosure of contingent assets and liabilities.
2. Summary of Significant Accounting Policies
Significant Accounting Policies
There have been no material changes to our significant accounting policies as compared to the significant accounting policies described in our Annual Report on Form 10-K for the fiscal year ended December 31, 2013.
Recently Issued Accounting Standards
In April 2014, the Financial Accounting Standards Board, or FASB, issued Accounting Standards Update (ASU) No. 2014-08, Reporting Discontinued Operations and Disclosures of Components of an Entity, which changes the criteria for determining which disposals can be presented as discontinued operations and modifies related disclosure requirements. The updated guidance defines discontinued operations as a disposal of a component or group of components that is disposed of or is classified as held for sale and represents a strategic shift that has (or will have) a major effect on an entity’s operations and financial results and expands the disclosure requirements for discontinued operations and adds new disclosures for individually significant dispositions that do not qualify as discontinued operations. ASU No. 2014-08 is effective for fiscal years, and interim reporting periods within those years, beginning after December 15, 2014. ASU No. 2014-08 would be applied to any future applicable transaction.
5
3. Business Combinations
Acquisition of Lemon
On December 11, 2013, we acquired Lemon, a mobile wallet innovator. In connection with this acquisition, we launched our new LifeLock mobile application. The aggregate purchase price consisted of approximately $42,369 of cash paid at the closing (net of cash acquired of $3,315). We preliminarily allocated the total purchase consideration to the assets acquired and liabilities assumed at their estimated fair values as of the date of acquisition, as determined by management, and, with respect to identifiable intangible assets, by management with the assistance of a valuation provided by a third-party valuation firm. We recorded the excess of the purchase price over the amounts allocated to assets acquired and liabilities assumed as goodwill in our consumer segment.
The allocation of the purchase price of the acquired assets and liabilities as of December 31, 2013 was based on provisional measurements of fair value as determined by management. Subsequent to the filing of our Annual Report on Form 10-K for the fiscal year ended December 31, 2013, we determined that approximately $4,988 of Lemon’s net operating loss carryforwards would expire as a result of limitations under Section 382 of the Internal Revenue Code. As such, we reduced deferred tax assets, net – noncurrent by $2,033, increasing goodwill. This adjustment has been reflected in the December 31, 2013 balances of deferred tax assets, net – noncurrent and goodwill in the accompanying condensed consolidated balance sheets.
We accounted for this acquisition using the acquisition method in accordance with Accounting Standards Codification, or ASC, 805, Business Combinations. Accordingly, we allocated the purchase price of the acquired assets and liabilities based on their estimated fair values as of the acquisition date as summarized in the following table:
Net assets assumed |
|
$ |
3,184 |
|
Deferred tax assets, net – noncurrent |
|
|
9,896 |
|
Intangible assets acquired |
|
|
3,880 |
|
Goodwill |
|
|
28,724 |
|
Total purchase price consideration |
|
$ |
45,684 |
|
4. Marketable Securities
The following is summary of marketable securities designated as available-for-sale as of March 31, 2014:
|
|
|
|
|
Gross |
|
|
Gross |
|
|
|
|
|
||
|
Amortized |
|
|
Unrealized |
|
|
Unrealized |
|
|
Estimated |
|
||||
|
Cost |
|
|
Gains |
|
|
Losses |
|
|
Fair Value |
|
||||
Corporate bonds |
$ |
34,247 |
|
|
$ |
- |
|
|
$ |
(19 |
) |
|
$ |
34,228 |
|
Municipal bonds |
|
12,798 |
|
|
|
1 |
|
|
|
(3 |
) |
|
|
12,796 |
|
Certificates of deposit |
|
498 |
|
|
|
- |
|
|
|
- |
|
|
|
498 |
|
Total marketable securities |
$ |
47,543 |
|
|
$ |
1 |
|
|
$ |
(22 |
) |
|
$ |
47,522 |
|
All marketable securities are classified as current regardless of contractual maturity dates because we consider such investments to represent cash available for current operations.
As of March 31, 2014, we did not consider any of our marketable securities to be other-than-temporarily impaired. When evaluating our investments for other-than-temporary impairment, we review factors such as the length of time and extent to which fair value has been below its cost basis, the financial condition of the issuer, our ability and intent to hold the security and whether it is more likely than not that we will be required to sell the investment before recovery of its cost basis.
6
The following is a summary of amortized cost and estimated fair value of marketable securities as of March 31, 2014, by maturity:
|
|
|
|
|
Gross |
|
|
Gross |
|
|
|
|
|
||
|
Amortized |
|
|
Unrealized |
|
|
Unrealized |
|
|
Estimated |
|
||||
|
Cost |
|
|
Gains |
|
|
Losses |
|
|
Fair Value |
|
||||
Due in one year or less |
$ |
47,543 |
|
|
$ |
1 |
|
|
$ |
(22 |
) |
|
$ |
47,522 |
|
Due after one year |
|
- |
|
|
|
- |
|
|
|
- |
|
|
|
- |
|
Total marketable securities |
$ |
47,543 |
|
|
$ |
1 |
|
|
$ |
(22 |
) |
|
$ |
47,522 |
|
The following is summary of marketable securities designated as available-as-sale as of December 31, 2013:
|
|
|
|
|
Gross |
|
|
Gross |
|
|
|
|
|
||
|
Amortized |
|
|
Unrealized |
|
|
Unrealized |
|
|
Estimated |
|
||||
|
Cost |
|
|
Gains |
|
|
Losses |
|
|
Fair Value |
|
||||
Corporate bonds |
$ |
37,399 |
|
|
$ |
1 |
|
|
$ |
(29 |
) |
|
$ |
37,371 |
|
Municipal bonds |
|
10,820 |
|
|
|
2 |
|
|
|
(3 |
) |
|
|
10,819 |
|
Certificates of deposit |
|
498 |
|
|
|
- |
|
|
|
- |
|
|
|
498 |
|
Total marketable securities |
$ |
48,717 |
|
|
$ |
3 |
|
|
$ |
(32 |
) |
|
$ |
48,688 |
|
The following is a summary of amortized cost and estimated fair value of marketable securities as of December 31, 2013, by maturity:
|
|
|
|
|
Gross |
|
|
Gross |
|
|
|
|
|
||
|
Amortized |
|
|
Unrealized |
|
|
Unrealized |
|
|
Estimated |
|
||||
|
Cost |
|
|
Gains |
|
|
Losses |
|
|
Fair Value |
|
||||
Due in one year or less |
$ |
47,398 |
|
|
$ |
3 |
|
|
$ |
(32 |
) |
|
$ |
47,369 |
|
Due after one year |
|
1,319 |
|
|
|
- |
|
|
|
- |
|
|
|
1,319 |
|
Total marketable securities |
$ |
48,717 |
|
|
$ |
3 |
|
|
$ |
(32 |
) |
|
$ |
48,688 |
|
5. Stockholders’ Equity
Share-Based Compensation
We issue stock-based awards to our employees in the form of stock options, restricted stock units, and restricted stock. We also have an employee stock purchase plan. The following table summarizes the components of share-based compensation expense included in our condensed consolidated statement of operations for the three-month periods ended March 31:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
|
(in thousands) |
|
|||||
Cost of services |
$ |
343 |
|
|
$ |
206 |
|
Sales and marketing |
|
894 |
|
|
|
333 |
|
Technology and development |
|
1,973 |
|
|
|
515 |
|
General and administrative |
|
2,265 |
|
|
|
1,670 |
|
Total share-based compensation |
$ |
5,475 |
|
|
$ |
2,724 |
|
Unrecognized share-based compensation expenses totaled $86,732 as of March 31, 2014, which we expect to recognize over a weighted-average time period of 3.2 years.
7
Stock Warrants
As of March 31, 2014, we had the following warrants to purchase common stock outstanding:
Expiration Date |
|
Shares |
|
|
Exercise |
|
||
October 3, 2014 |
|
|
2,334,044 |
|
|
|
0.70 |
|
December 19, 2014 |
|
|
166,666 |
|
|
|
4.50 |
|
6. Fair Value Measurements
As of March 31, 2014 and December 31, 2013, the fair value of our financial assets was as follows:
|
Level 1 |
|
|
Level 2 |
|
|
Level 3 |
|
|
Total |
|
||||
March 31, 2014 |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Assets: |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Commercial paper (1) |
$ |
- |
|
|
$ |
45,134 |
|
|
$ |
- |
|
|
$ |
45,134 |
|
Money market funds (1) |
|
2,036 |
|
|
|
- |
|
|
|
- |
|
|
|
2,036 |
|
Corporate bonds (2) |
|
- |
|
|
|
34,228 |
|
|
|
- |
|
|
|
34,228 |
|
Municipal bonds (2) |
|
- |
|
|
|
12,796 |
|
|
|
- |
|
|
|
12,796 |
|
Certificates of deposit (2) |
|
- |
|
|
|
498 |
|
|
|
- |
|
|
|
498 |
|
Total assets measured at fair value |
$ |
2,036 |
|
|
$ |
92,656 |
|
|
$ |
- |
|
|
$ |
94,692 |
|
December 31, 2013 |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Assets: |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Commercial paper (1) |
$ |
- |
|
|
$ |
45,110 |
|
|
$ |
- |
|
|
$ |
45,110 |
|
Money market funds (1) |
|
911 |
|
|
|
- |
|
|
|
- |
|
|
|
911 |
|
Corporate bonds (2) |
|
- |
|
|
|
37,371 |
|
|
|
- |
|
|
|
37,371 |
|
Municipal bonds (2) |
|
- |
|
|
|
10,819 |
|
|
|
- |
|
|
|
10,819 |
|
Certificates of deposit (2) |
|
- |
|
|
|
498 |
|
|
|
- |
|
|
|
498 |
|
Total assets measured at fair value |
$ |
911 |
|
|
$ |
93,798 |
|
|
$ |
- |
|
|
$ |
94,709 |
|
(1) | Classified in cash and cash equivalents |
(2) | Classified in marketable securities |
The fair values of our cash equivalents and available-for-sale securities included in the Level 1 and Level 2 categories are obtained from an independent pricing service, which uses a model driven valuation technique using observable market data or inputs corroborated by observable market data.
7. Net Loss Per Share
The following table sets forth the computation of basic and diluted net loss per share attributable to common stockholders for the three-month periods ended March 31:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
Net loss |
$ |
(5,169 |
) |
|
$ |
(4,117 |
) |
Denominator (basic and diluted): |
|
|
|
|
|
|
|
Weighted average common shares outstanding |
|
91,903,036 |
|
|
|
86,639,538 |
|
Net loss attributable per share to common stockholders: |
|
|
|
|
|
|
|
Basic |
$ |
(0.06 |
) |
|
$ |
(0.05 |
) |
Diluted |
$ |
(0.06 |
) |
|
$ |
(0.05 |
) |
8
For the three-month periods ended March 31, 2014 and 2013, potentially dilutive securities are not included in the calculation of diluted loss per share as their impact would be anti-dilutive. The following weighted-average number of outstanding stock options, restricted stock units and restricted stock awards, common equivalent shares from stock warrants, and shares purchased under our Employee Stock Purchase Plan, or ESPP, were excluded from the computation of diluted net loss per share for the three-month periods ended March 31:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
Stock options outstanding |
|
4,475,301 |
|
|
|
5,562,516 |
|
Restricted stock units and restricted stock awards |
|
217,010 |
|
|
|
49,484 |
|
Common equivalent shares from stock warrants |
|
2,378,641 |
|
|
|
2,322,597 |
|
Shares purchased under ESPP |
|
25,105 |
|
|
|
5,783 |
|
|
|
7,096,057 |
|
|
|
7,940,380 |
|
8. Segment Reporting
Following our acquisition of ID Analytics in the first quarter of 2012, we began operating our business and reviewing and assessing our operating performance using two reportable segments: our consumer segment and our enterprise segment. In our consumer segment, we offer proactive identity theft protection services to our members on an annual or monthly subscription basis. In our enterprise segment, we offer fraud and risk solutions to our enterprise customers.
Financial information about our segments during the three-month period ended March 31, 2014 and as of March 31, 2014 was as follows:
|
Consumer |
|
|
Enterprise |
|
|
Eliminations |
|
|
Total |
|
||||
Revenue |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
External customers |
$ |
100,995 |
|
|
$ |
6,591 |
|
|
$ |
- |
|
|
$ |
107,586 |
|
Intersegment revenue |
|
- |
|
|
|
1,514 |
|
|
|
(1,514 |
) |
|
|
- |
|
Loss from operations |
|
(4,523 |
) |
|
|
(4,156 |
) |
|
|
- |
|
|
|
(8,679 |
) |
Goodwill |
|
98,615 |
|
|
|
59,537 |
|
|
|
- |
|
|
|
158,152 |
|
Total assets |
|
376,457 |
|
|
|
111,073 |
|
|
|
(515 |
) |
|
|
487,015 |
|
Financial information about our segments during the three-month period ended March 31, 2013 and as of December 31, 2013 was as follows:
|
Consumer |
|
|
Enterprise |
|
|
Eliminations |
|
|
Total |
|
||||
Revenue |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
External customers |
$ |
75,094 |
|
|
$ |
7,001 |
|
|
$ |
- |
|
|
$ |
82,095 |
|
Intersegment revenue |
|
- |
|
|
|
1,237 |
|
|
|
(1,237 |
) |
|
|
- |
|
Loss from operations |
|
(633 |
) |
|
|
(3,283 |
) |
|
|
- |
|
|
|
(3,916 |
) |
Goodwill |
|
98,615 |
|
|
|
59,537 |
|
|
|
- |
|
|
|
158,152 |
|
Total assets |
|
349,394 |
|
|
|
114,337 |
|
|
|
(481 |
) |
|
|
463,250 |
|
We allocated goodwill between our segments by estimating the expected synergies to each segment.
We derive all of our revenue from sales in the United States, and substantially all of our long-lived assets are located in the United States.
9. Income Taxes
Income taxes for the interim periods presented have been included in the accompanying condensed consolidated financial statements on the basis of an estimated annual effective tax rate. Based on an estimated annual effective tax rate and discrete items, the estimated income tax (benefit) expense from operations for the three-month periods ended March 31, 2014 and 2013 was approximately $(3,548) and $150, respectively. The determination of the interim period income tax provision utilizes the effective tax
9
rate method, which requires us to estimate certain annualized components of the calculation of the income tax provision, including the annual effective tax rate by entity and jurisdiction.
In the fourth quarter of 2013, in connection with the acquisition of Lemon and the preliminary purchase price allocation, we analyzed Lemon’s prior ownership changes, including the change which arose as a result of our acquisition of Lemon. As a result of the preliminary analysis, we estimated that none of Lemon’s net operating loss carryforwards would expire as a result of limitations under Section 382 of the Internal Revenue Code. Subsequent to the filing of our Annual Report on Form 10-K for the fiscal year ended December 31, 2013, we received responses from certain former shareholders who had held a 5% or greater ownership interest in Lemon prior to the acquisition and determined that due to the ownership changes of those former shareholders, approximately $4,988 of Lemon’s net operating loss carryforwards will expire solely as a result of the Section 382 limitations. As such, we retrospectively adjusted our preliminary purchase price allocation to reflect this information.
10. Contingencies
As part of our consumer services, we offer 24x7x365 member service support. If a member’s identity has been compromised, our member service team and remediation specialists will assist the member until the issue has been resolved. This includes our $1 million service guarantee, which is backed by an identity theft insurance policy, under which we will spend up to $1 million to cover certain third-party costs and expenses incurred in connection with the remediation, such as legal and investigatory fees. This insurance also covers certain out-of-pocket expenses, such as loss of income, replacement of fraudulent withdrawals, and costs associated with child and elderly care, travel, and replacement of documents. While we have reimbursed members for claims under this guarantee, the amounts in aggregate for the three-month periods ended March 31, 2014 and 2013 were not material.
In September 2012, Denise Richardson filed a complaint against our company and Todd Davis. Ms. Richardson claims that she was improperly classified as an independent contractor instead of an employee and that we breached the terms of an alleged employment agreement. Ms. Richardson claims she is entitled to equitable relief, compensatory damages, liquidated damages, statutory penalties, punitive damages, interest, costs, and attorneys’ fees. On March 31, 2014, our motion to dismiss was granted in part and denied in part with the court dismissing nine of the ten counts that were subject to the motion to dismiss, including the single count against Mr. Davis. On April 23, 2014, Ms. Richardson filed an amended complaint against our company and Mr. Davis again claiming that she was improperly classified as an independent contractor instead of an employee and that we breached the terms of an alleged employment agreement. Ms. Richardson claims she is entitled to equitable relief, compensatory damages, liquidated damages, statutory penalties, punitive damages, interest, costs, and attorneys’ fees. On April 29, 2014, Mr. Davis and we filed a motion to dismiss all but one of the counts in such amended complaint. Ms. Richardson’s response is due on May 16, 2014..
On March 3, 2014, Dawn B. Bien, representing herself and seeking to represent a class of persons who acquired our securities from February 26, 2013 to February 19, 2014, inclusive, or the Class Period, filed a complaint in United States District Court for the District of Arizona against us, Todd Davis, and Chris Power. We refer to this complaint as the Bien Complaint. The Bien Complaint alleges that we and Messrs. Davis and Power, in violation of Sections 10(b) and 20(a) of the Securities Exchange Act of 1934, as amended, or the Exchange Act, disseminated materially false or misleading information, or failed to disclose material facts during the Class Period in connection with our business and our operational and compliance policies, including our and Mr. Davis’s compliance with the Stipulated Final Judgment and Order for Permanent Injunction and Other Equitable Relief entered into in March 2010 with the Federal Trade Commission, or the FTC Order, wherein we settled allegations by the Federal Trade Commission challenging certain of our advertising and marketing. The Bien Complaint also contends that as a result of alleged violations of governmental laws, regulations, and the FTC Order, our financial statements were materially false and misleading at all relevant times. The Bien Complaint seeks certification as a class action, compensatory damages, and attorneys’ fees and costs. On March 10, 2014, Joseph F. Scesny, representing himself and seeking to represent a class of persons who acquired our securities from February 26, 2013 to February 19, 2014, inclusive, filed a complaint in United States District Court for the District of Arizona against us, Todd Davis, and Chris Power. We refer to this complaint as the Scesny Complaint. The Scesny Complaint is substantially similar to the Bien Complaint and seeks substantially similar relief. We anticipate that the Bien Complaint and Scesny Complaint will be consolidated into one action and that the court will select a lead plaintiff as provided by the federal securities laws governing purported class action cases.
On March 13, 2014, we received a request from the Federal Trade Commission, or the FTC, for documents and information related to our compliance with the FTC Order. Prior to our receipt of the FTC’s request, we met with FTC Staff on January 17, 2014, at our request, to discuss issues regarding allegations that have been asserted in a whistleblower claim against us relating to our compliance with the FTC Order. We are cooperating with the FTC in regards to its request and are currently in the process of providing the documents and information requested by the FTC.
On March 20, 2014, Michael D. Peters filed a complaint in United States District Court for the District of Arizona against our company, Kim Jones, and Cristy Schaan. Mr. Jones is not affiliated with us. Ms. Schaan is our Chief Information Security Officer. In his complaint, Mr. Peters alleges that we violated the whistleblower protection provisions of the Sarbanes-Oxley Act of
10
2002, or the Sarbanes-Oxley Act, and the Dodd-Frank Wall Street Reform and Consumer Protection Act, or the Dodd-Frank Act, by terminating Mr. Peters’ employment as a result of alleged disclosures that he made to us, and that Ms. Schaan defamed Mr. Peters. Mr. Peters seeks from us two times his back pay, two times the value of certain stock options and bonus, moving expenses, damages for emotional harm and anxiety, damages for harm to reputation, litigation costs including attorneys’ fees, and interest, and seeks from Ms. Schaan actual damages, punitive damages, and interest. On April 21, 2014, we filed an answer, affirmative defenses, and counterclaims, answering Mr. Peters’ claim under the Sarbanes-Oxley Act and asserting counterclaims against Mr. Peters for fraud, negligent misrepresentation, breach of contract, and unjust enrichment, based on our allegations that we were induced to hire Mr. Peters by his false statements and misrepresentations regarding his employment history and seeking to recover actual and consequential damages, punitive damages, attorneys’ fees, and the $15 signing bonus paid to Mr. Peters. Mr. Peters’ response to the counterclaim is due on May 8, 2014. On April 21, 2014, we also filed a motion to dismiss Mr. Peters’ claim under the Dodd-Frank Act. Mr. Peters’ response to that motion to dismiss is due on May 15, 2014. On April 25, 2014, Ms. Schaan filed a motion to dismiss Mr. Peters’ claim against her. Mr. Peters’ response to that motion to dismiss is due on May 12, 2014.
We are subject to other legal proceedings and claims that have arisen in the ordinary course of business. Although there can be no assurance as to the ultimate disposition of these matters and the proceedings disclosed above, we believe, based upon the information available at this time, that a material adverse outcome related to the matters is neither probable nor estimable.
11
Item 2. Management’s Discussion and Analysis of Financial Condition and Results of Operations.
You should read the following discussion of our financial condition and results of operations in conjunction with the condensed consolidated financial statements and the notes thereto included elsewhere in this Quarterly Report on Form 10-Q and with our audited consolidated financial statements included in our Annual Report on Form 10-K for the fiscal year ended December 31, 2013. This Quarterly Report on Form 10-Q contains “forward-looking statements” that involve substantial risks and uncertainties. The statements contained in this Quarterly Report on Form 10-Q that are not purely historical are forward-looking statements within the meaning of Section 27A of the Securities Act of 1933, as amended, or the Securities Act, and Section 21E of the Exchange Act, including, but not limited to, statements regarding our expectations, beliefs, intentions, strategies, future operations, future financial position, future revenue, projected expenses, and plans and objectives of management. In some cases, you can identify forward-looking statements by terms such as “anticipate,” “believe,” “estimate,” “expect,” “intend,” “may,” “might,” “plan,” “project,” “will,” “would,” “should,” “could,” “can,” “predict,” “potential,” “continue,” “objective,” or the negative of these terms, and similar expressions intended to identify forward-looking statements. However, not all forward-looking statements contain these identifying words. These forward-looking statements reflect our current views about future events and involve known risks, uncertainties, and other factors that may cause our actual results, levels of activity, performance, or achievement to be materially different from those expressed or implied by the forward-looking statements. Factors that could cause or contribute to such differences include, but are not limited to, those identified below, and those discussed in the section titled “Risk Factors” included in this Quarterly Report on Form 10-Q and our Annual Report on Form 10-K for the fiscal year ended December 31, 2013. Furthermore, such forward-looking statements speak only as of the date of this report. Except as required by law, we undertake no obligation to update any forward-looking statements to reflect events or circumstances after the date of such statements.
Overview
We are a leading provider of proactive identity theft protection services for consumers and fraud and risk solutions for enterprises. We protect our members by constantly monitoring identity-related events, such as new account openings and credit-related applications. If we detect that a member’s personally identifiable information is being used, we offer notifications and alerts, including proactive, near real-time, actionable alerts that provide our members peace of mind that we are monitoring use of their identity and allow our members to confirm valid or unauthorized identity use. If a member confirms that the use of his or her identity is unauthorized, we can proactively take actions designed to protect the member’s identity. We also provide remediation services to our members in the event that an identity theft actually occurs. We protect our enterprise customers by delivering on-demand identity risk and authentication information about consumers. Our enterprise customers utilize this information in real time to make decisions about opening or modifying accounts and providing products, services, or credit to consumers to reduce financial losses from identity fraud.
The foundation of our differentiated services is the LifeLock ecosystem. This ecosystem combines large data repositories of personally identifiable information and consumer transactions, proprietary predictive analytics, and a highly scalable technology platform. Our members and enterprise customers enhance our ecosystem by continually contributing to the identity and transaction data in our repositories. We apply predictive analytics to the data in our repositories to provide our members and enterprise customers actionable intelligence that helps protect against identity theft and identity fraud. As a result of our combination of scale, reach, and technology, we believe that we have the most proactive and comprehensive identity theft protection services available, as well as the most recognized brand in the identity theft protection services industry.
On December 11, 2013, we acquired mobile wallet innovator Lemon for approximately $42.4 million in cash and launched our new LifeLock Wallet mobile application. The LifeLock Wallet mobile application allows consumers to replicate and store a digital copy of their personal wallet contents on their smart device for records backup, as well as transaction monitoring and mobile use of items such as credit, identification, ATM, insurance, and loyalty cards. The LifeLock Wallet mobile application also offers our members one-touch access to our identity theft protection services.
We derive the substantial majority of our revenue from member subscription fees. We also derive revenue from transaction fees from our enterprise customers.
We offer our consumer identity theft protection services on a monthly or annual subscription basis. We currently offer our consumer services under our basic LifeLock, LifeLock Command Center, LifeLock Junior, and premium LifeLock Ultimate services. Our average revenue per member is lower than our retail list prices due to wholesale or bulk pricing that we offer to strategic partners in our embedded product, employee benefits, and breach distribution channels to drive our membership growth. In our embedded product channel, our strategic partners embed our consumer services into their products and services and pay us on behalf of their customers; in our employee benefit channel, our strategic partners offer our consumer services as a voluntary benefit as part of their employee benefit enrollment process; and in our breach channel, enterprises that have experienced a data breach pay us a fee to provide our services to the victims of the data breach. We also offer special discounts and promotions from time to time to incentivize prospective members to enroll in one of our consumer services. Our members pay us the full subscription fee at the beginning of each
12
subscription period, in most cases by authorizing us to directly charge their credit or debit cards. We initially record the subscription fee as deferred revenue and then recognize it ratably on a daily basis over the subscription period. The prepaid subscription fees enhance our visibility of revenue and allow us to collect cash prior to paying our fulfillment partners.
Our enterprise customers pay us based on their monthly volume of transactions with us, with approximately 30% of them committed to monthly transaction minimums. We recognize revenue at the end of each month based on transaction volume for that month and bill our enterprise customers at the conclusion of each month.
We have historically invested significantly in new member acquisition and expect to continue to do so for the foreseeable future. Our largest operating expense is advertising for member acquisition, which we record as a sales and marketing expense. This is comprised of radio, television, and print advertisements; direct mail campaigns; online display advertising; paid search and search-engine optimization; third-party endorsements; and education programs. We also pay internal and external sale commissions, which we record as a sales and marketing expense. In general, increases in revenue and cumulative ending members occur during and after periods of significant and effective direct retail marketing efforts.
Our revenue grew from $82.1 million for the three-month period ended March 31, 2013 to $107.6 million for the three-month period ended March 31, 2014, an increase of 31%, including year-over-year growth within our consumer segment of 34%. We generated a loss from operations of $8.7 million and a net loss of $5.2 million for the three-month period ended March 31, 2014.
Our Business Model
Following our acquisition of ID Analytics in the first quarter of 2012, we began operating our business and reviewing and assessing our operating performance using two reportable segments: our consumer segment and our enterprise segment. We review and assess our operating performance using segment revenue, income (loss) from operations, and total assets. These performance measures include the allocation of operating expenses to our reportable segments based on management’s specific identification of costs associated to those segments.
Consumer Services
We evaluate the lifetime value of a member relationship over its anticipated lifecycle. While we generally incur member acquisition costs in advance of or at the time of the acquisition of the member, we recognize revenue ratably over the subscription period. As a result, a member relationship is not profitable at the beginning of the subscription period even though it is likely to have value to us over the lifetime of the member relationship.
When a member’s subscription automatically renews in each successive period, the relative value of that member increases because we do not incur significant incremental acquisition costs. We also benefit from decreasing fulfillment and member support costs related to that member, as well as economies of scale in our capital and operating and other support expenditures.
Enterprise Services
In our enterprise business, the majority of our costs relate to personnel primarily responsible for data analytics, data management, software development, sales and operations, and various support functions. We incur minimal third-party data expenses, as our enterprise customers typically provide us with their customer transaction data as part of our service. New customer acquisition is often a lengthy process requiring significant investment in the sales team, including costs related to detailed retrospective data analysis to demonstrate the return on investment to prospective customers had our services been deployed over a specific period of time. Since most of the expenses in our enterprise business are fixed in nature, as we add new enterprise customers, there are typically modest incremental costs resulting in additional economies of scale.
Key Metrics
We regularly review a number of operating and financial metrics to evaluate our business, determine the allocation of our resources, measure the effectiveness of our sales and marketing efforts, make corporate strategy decisions, and assess operational efficiencies.
13
Key Operating Metrics
The following table summarizes our key operating metrics for the three-month periods ended March 31:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
|
(in thousands, except percentages and per member data) |
|
|||||
|
(Unaudited) |
|
|||||
Cumulative ending members |
|
3,221 |
|
|
|
2,636 |
|
Gross new members |
|
344 |
|
|
|
249 |
|
Member retention rate |
|
87.5 |
% |
|
|
87.2 |
% |
Average cost of acquisition per member |
$ |
156 |
|
|
$ |
156 |
|
Monthly average revenue per member |
$ |
10.81 |
|
|
$ |
9.80 |
|
Enterprise transactions |
|
52,709 |
|
|
|
58,483 |
|
Cumulative ending members. We calculate cumulative ending members as the total number of members at the end of the relevant period. Most of our members are paying subscribers who have enrolled in our consumer services directly with us on a monthly or annual basis. A small percentage of our members receive our consumer services through third-party enterprises that pay us directly, often as a result of a breach within the enterprise or by embedding our service within a broader third- party offering. We monitor cumulative ending members because it provides an indication of the revenue and expenses that we expect to recognize in the future.

As of March 31, 2014, we had approximately 3.2 million cumulative ending members, an increase of 22% from March 31, 2013. This increase was driven by several factors, including the success of our marketing campaigns, increased awareness of data breaches, media coverage of identity theft, and our continued strong annual retention rate.
Gross new members. We calculate gross new members as the total number of new members who enroll in one of our consumer services during the relevant period. Many factors may affect the volume of gross new members in each period, including the effectiveness of our marketing campaigns, the timing of our marketing programs, the effectiveness of our strategic partnerships, and the general level of identity theft coverage in the media. We monitor gross new members because it provides an indication of the revenue and expenses that we expect to recognize in the future. For the three-month period ended March 31, 2014, we enrolled approximately 344,000 gross new members, up from approximately 249,000 for the three-month period ended March 31, 2013. This increase was driven by the success of our marketing campaigns, the continued success of our LifeLock Ultimate service, which accounted for more than 40% our gross new members during the three-month period ended March 31, 2014, and increased awareness of data breaches and identity theft.
14
Member retention rate. We define member retention rate as the percentage of members on the last day of the prior year who remain members on the last day of the current year, or for quarterly presentations, the percentage of members on the last day of the comparable quarterly period in the prior year who remain members on the last day of the current quarterly period. A number of factors may increase our member retention rate, including increases in the number of members enrolled on an annual subscription, increases in the number of alerts a member receives, and increases in the number of members enrolled through strategic partners with which the member has a strong association. Conversely, factors reducing our member retention rate may include increases in the number of members enrolled on a monthly subscription, and the end of programs in our embedded product and breach channels. In addition, the length of time a member has been enrolled in one of our services will impact our member retention rate. Historically, the member retention rate for our premium services has been lower than the member retention rate for our LifeLock Basic service, which we believe is driven primarily by price.

As of March 31, 2014, our member retention rate was 87.5%, which was our sixth consecutive quarter above 87%. The decrease in retention rate from the fourth quarter of 2013 was driven, in part, by the cancellation of breach members who enrolled in previous years and the impact of an increased number of member credit and debit cards that were replaced as a result of large data breaches in the fourth quarter of 2013.
Average cost of acquisition per member. We calculate average cost of acquisition per member as our sales and marketing expense for our consumer segment during the relevant period divided by our gross new members for the period. A number of factors may influence this metric, including shifts in the mix of our media spend. For example, when we engage in marketing efforts to build our brand, our cost of acquisition per member increases in the short term with the expectation that it will decrease over the long term. In addition, when we introduce new partnerships in our embedded product channel, such as our partnership with AOL in the fourth quarter of 2011, our average cost of acquisition per member decreases due to the volume of members that enroll in our consumer services in a relatively short period of time. We monitor average cost of acquisition per member to evaluate the efficiency of our marketing programs in acquiring new members. For the three-month periods ended March 31, 2014 and 2013, our average cost of acquisition per member was $156. Our member retention rate and the increasing monthly average revenue per member, primarily from the continued penetration of our LifeLock Ultimate service, results in a higher lifetime value of a member relationship which enables us to absorb a higher average cost of acquisition per member.
15
Monthly average revenue per member. We calculate monthly average revenue per member as our consumer revenue during the relevant period divided by the average number of cumulative ending members during the relevant period (determined by taking the average of the cumulative ending members at the beginning of the relevant period and the cumulative ending members at the end of each month in the relevant period), divided by the number of months in the relevant period. A number of factors may influence this metric, including whether a member enrolls in one of our premium services; whether we offer the member any promotional discounts upon enrollment; the distribution channel through which we acquire the member, as we offer wholesale pricing in our embedded product, employee benefit, and breach channels; and whether a new member subscribes on a monthly or annual basis, as members enrolling on an annual subscription receive a discount for paying for a year in advance. While our retail list prices have historically remained unchanged, our average revenue per member for the three-month period ended March 31, 2014 increased approximately 10% from the three month period ended March, 31, 2013. This growth was primarily driven by increased adoption of our higher priced premium services by a greater percentage of our members, a trend we expect will continue. We monitor monthly average revenue per member because it is a strong indicator of revenue in our consumer business and of the performance of our premium services. The increase in our monthly average revenue per member resulted primarily from the continued success of our LifeLock Ultimate service, which accounted for more than 40% of our gross new members for the three month period ended March 31, 2014.
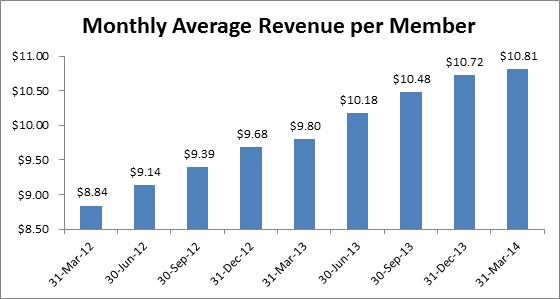
Our monthly average revenue per member for the three-month period ended March 31, 2014 was $10.81, an increase of 10% from the three-month period ended March 31, 2013.
Enterprise transactions. We calculate enterprise transactions as the total number of enterprise transactions processed for either an identity risk or credit risk score during the relevant period. Our enterprise transactions are processed by ID Analytics, which we acquired in the first quarter of 2012. Accordingly, the enterprise transactions data includes transactions processed by ID Analytics before the acquisition. Enterprise transactions have historically been higher in the fourth quarter as the level of credit applications and general consumer spending increases. We monitor the volume of enterprise transactions because it is a strong indicator of revenue in our enterprise business.
We processed 52.7 million enterprise transactions for the three-month period ended March 31, 2014, a decrease of 10% from the three-month period ended March 31, 2013. The reduction in enterprise transactions related to us giving notice of non-renewal to several customers who compete in our consumer business and allowing such contracts to lapse. In addition, in the quarter ended June 30, 2013 we had a large telecommunications customer stop scoring their new wireline customers due to low levels of fraud in the business line. While we were able to reengage and commence scoring a portion of the volume in the quarter ended March 31, 2014, there was still a reduction year over year from this customer.
16
Key Financial Metrics
The following table summarizes our key financial metrics for the three-month periods ended March 31:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
|
(in thousands) |
|
|||||
Consumer revenue |
$ |
100,995 |
|
|
$ |
75,094 |
|
Enterprise revenue |
|
6,591 |
|
|
|
7,001 |
|
Total revenue |
|
107,586 |
|
|
|
82,095 |
|
Adjusted net income (loss) |
|
(1,014 |
) |
|
|
573 |
|
Adjusted EBITDA |
|
657 |
|
|
|
1,879 |
|
Free cash flow |
|
14,389 |
|
|
|
11,510 |
|
Adjusted Net Income (Loss)
Adjusted net income (loss) is a non-GAAP financial measure that we calculate as net income (loss) excluding amortization of acquired intangible assets, share-based compensation, income tax benefits and expenses resulting from changes in our deferred tax assets, and acquisition related expenses. Historically, we also excluded from net income (loss) changes in fair value of warrant liabilities and change in fair value of embedded derivatives in the periods in which those items occurred. We do not currently have any warrant liabilities or embedded derivatives; accordingly, we will only include those items of income and expense in our reconciliation of adjusted net income (loss) for period-over-period comparisons. We have included adjusted net income (loss) in this Quarterly Report on Form 10-Q because it is a key measure used by us to understand and evaluate our core operating performance and trends. In particular, the exclusion of certain expenses in calculating adjusted net income (loss) can provide a useful measure for period-to-period comparisons of our core business.
Accordingly, we believe that adjusted net income (loss) provides useful information to investors and others in understanding and evaluating our operating results in the same manner as we do. We believe the exclusion of certain items of income and expense from net income (loss) in calculating adjusted net income (loss) is useful because (i) the amount of such income and expense in any specific period may not directly correlate to the underlying operational performance of our business, and/or (ii) such income and expense can vary significantly between periods as a result of new acquisitions and full amortization of previously acquired intangible assets.
Our use of adjusted net income (loss) has limitations as an analytical tool, and you should not consider it in isolation or as a substitute for analysis of our operating results as reported under GAAP. Some of these limitations include the following:
· | although amortization of intangible assets is a non-cash charge, additional intangible assets may be acquired in the future and adjusted net income (loss) does not reflect cash capital expenditure requirements for new acquisitions; |
· | adjusted net income (loss) does not reflect the cash requirements for new acquisitions; |
· | adjusted net income (loss) does not reflect changes in, or cash requirements for, our working capital needs; |
· | adjusted net income (loss) does not consider the potentially dilutive impact of share-based compensation; |
· | adjusted net income (loss) does not reflect the deferred income tax benefit from the release of the valuation allowance or income tax expenses which reduce our deferred tax asset for net operating losses or other net changes in deferred tax assets; |
· | adjusted net income (loss) does not reflect the expenses incurred for new acquisitions; and |
· | other companies, including companies in our industry, may calculate adjusted net income (loss) or similarly titled measures differently, limiting their usefulness as a comparative measure. |
17
Because of these limitations, you should consider adjusted net income (loss) alongside other financial performance measures, including various cash flow metrics, net income (loss), and our other GAAP results. The following table presents a reconciliation of net loss to adjusted net income (loss) for applicable items of income and expense that impacted each of the periods indicated:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
|
(in thousands) |
|
|||||
Reconciliation of Net Loss to Adjusted Net Income (Loss): |
|
|
|
|
|
|
|
Net loss |
$ |
(5,169 |
) |
|
$ |
(4,117 |
) |
Amortization of acquired intangible assets |
|
2,231 |
|
|
|
1,966 |
|
Share-based compensation |
|
5,475 |
|
|
|
2,724 |
|
Deferred income tax benefit |
|
(3,551 |
) |
|
|
- |
|
Adjusted net income (loss) |
$ |
(1,014 |
) |
|
$ |
573 |
|
Adjusted EBITDA
Adjusted EBITDA is a non-GAAP financial measure that we calculate as net income (loss) excluding depreciation and amortization, share-based compensation, interest expense, interest income, other income (expense), income tax (benefit) expense, and acquisition related expenses. Historically, we also excluded from net income (loss) changes in fair value of warrant liabilities and change in fair value of embedded derivatives in the periods in which those items occurred. We do not currently have any warrant liabilities or embedded derivatives; accordingly, we will only include those items of income and expense in our reconciliation of adjusted EBITDA for period-over-period comparisons. We have included adjusted EBITDA in this Quarterly Report on Form 10-Q because it is a key measure used by us to understand and evaluate our core operating performance and trends, to prepare and approve our annual budget, and to develop short- and long-term operational plans. In particular, the exclusion of certain expenses in calculating adjusted EBITDA can provide a useful measure for period-to-period comparisons of our core business. Additionally, adjusted EBITDA is a key financial measure used in determining management’s incentive compensation.
Accordingly, we believe that adjusted EBITDA provides useful information to investors and others in understanding and evaluating our operating results in the same manner as we do. We believe the exclusion of certain items of income and expense from net income (loss) in calculating adjusted EBITDA is useful because (i) the amount of such income and expense in any specific period may not directly correlate to the underlying operational performance of our business, and/or (ii) such income and expense can vary significantly between periods as a result of new acquisitions and full amortization of previously acquired intangible assets.
Our use of adjusted EBITDA has limitations as an analytical tool, and you should not consider it in isolation or as a substitute for analysis of our operating results as reported under GAAP. Some of these limitations include the following:
· | although depreciation and amortization are non-cash charges, the assets being depreciated and amortized may have to be replaced in the future, and adjusted EBITDA does not reflect cash capital expenditure requirements for such replacements or for new capital expenditure requirements; |
· | adjusted EBITDA does not reflect changes in, or cash requirements for, our working capital needs; |
· | adjusted EBITDA does not consider the potentially dilutive impact of share-based compensation; |
· | adjusted EBITDA does not reflect cash interest income or expense; |
· | adjusted EBITDA does not reflect tax payments that may represent a reduction in cash available to us; |
· | adjusted EBITDA does not reflect the expenses incurred for new acquisitions; and |
· | other companies, including companies in our industry, may calculate adjusted EBITDA or similarly titled measures differently, limiting their usefulness as a comparative measure. |
18
Because of these limitations, you should consider adjusted EBITDA alongside other financial performance measures, including various cash flow metrics, net income (loss), and our other GAAP results. The following table presents a reconciliation of net loss to adjusted EBITDA for applicable items of income and expense that impacted each of the periods indicated:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
|
(in thousands) |
|
|||||
Reconciliation of Net Loss to Adjusted EBITDA: |
|
|
|
|
|
|
|
Net loss |
$ |
(5,169 |
) |
|
$ |
(4,117 |
) |
Depreciation and amortization |
|
3,861 |
|
|
|
3,071 |
|
Share-based compensation |
|
5,475 |
|
|
|
2,724 |
|
Interest expense |
|
87 |
|
|
|
67 |
|
Interest income |
|
(60 |
) |
|
|
(20 |
) |
Other expense |
|
11 |
|
|
|
4 |
|
Income tax (benefit) expense |
|
(3,548 |
) |
|
|
150 |
|
Adjusted EBITDA |
$ |
657 |
|
|
$ |
1,879 |
|
Free Cash Flow
Free cash flow is a non-GAAP financial measure that we calculate as net cash provided by (used in) operating activities less net cash used in investing activities for acquisitions of property and equipment. We use free cash flow as a measure of our operating performance; for planning purposes, including the preparation of our annual operating budget; to allocate resources to enhance the financial performance of our business; to evaluate the effectiveness of our business strategies; to provide consistency and comparability with past financial performance; to determine capital requirements; to facilitate a comparison of our results with those of other companies; and in communications with our board of directors concerning our financial performance.
We use free cash flow to evaluate our business because, although it is similar to net cash provided by (used in) operating activities, we believe it typically presents a more conservative measure of cash flow as purchases of property and equipment are necessary components of ongoing operations. We believe that this non-GAAP financial measure is useful in evaluating our business because free cash flow reflects the cash surplus available to fund the expansion of our business after payment of capital expenditures relating to the necessary components of ongoing operations. We also believe that the use of free cash flow provides consistency and comparability with our past financial performance, facilitates period-to-period comparisons of operations, and also facilitates comparisons with other companies, many of which use similar non-GAAP financial measures to supplement their GAAP results.
Although free cash flow is frequently used by investors in their evaluations of companies, free cash flow has limitations as an analytical tool, and you should not consider it in isolation or as a substitute for analysis of our operating results as reported under GAAP. Some of these limitations include the following:
· | free cash flow does not reflect our future requirements for contractual commitments to third- party providers; |
· | free cash flow does not reflect the non-cash component of employee compensation or depreciation and amortization of property and equipment; and |
· | other companies, including companies in our industry, may calculate free cash flow or similarly titled measures differently, limiting their usefulness as comparative measures. |
19
Because of these limitations, you should consider free cash flow alongside other financial performance measures, including net cash provided by operating activities, net income (loss), and our other GAAP results. The following table presents a reconciliation of net cash provided by operating activities to free cash flow for each of the periods indicated:
|
For the Three Months Ended March 31, |
|
|||||
|
2014 |
|
|
2013 |
|
||
|
(in thousands) |
|
|||||
Reconciliation of Net Cash Provided By Operating Activities to Free Cash Flow: |
|
|
|
|
|
|
|
Net cash provided by operating activities |
$ |
18,316 |
|
|
$ |
12,795 |
|
Acquisitions of property and equipment |
|
(3,927 |
) |
|
|
(1,285 |
) |
Free cash flow |
$ |
14,389 |
|
|
$ |
11,510 |
|
Factors Affecting Our Performance
Customer acquisition costs. We expect to continue to make significant expenditures to grow our member and enterprise customer bases. Our average cost of acquisition per member and the number of new members we generate depends on a number of factors, including the effectiveness of our marketing campaigns, changes in cost of media, the competitive environment in our markets, the prevalence of identity theft issues in the media, publicity about our company, and the level of differentiation of our services. Shifts in the mix of our media spend also influence our member acquisition costs. For example, when we engage in marketing efforts to build our brand, our member acquisition costs increase in the short term with the expectation that they will decrease over the long term. We also continually test new media outlets, marketing campaigns, and call center scripting, each of which impacts our average cost of acquisition per member. In addition, given the success of our LifeLock Ultimate service since its launch in the fourth quarter of 2011, we expect to be able to absorb a higher average cost of acquisition per member and still recognize value over the lifetime of our member relationships.
Mix of members by services, billing cycle, and distribution channel. Our performance is affected by the mix of members subscribing to our various consumer services, by billing cycle (annual versus monthly), and by the distribution channel through which we acquire the member. Our adjusted EBITDA, adjusted net income (loss), free cash flow, and average cost of acquisition per member are all affected by this mix. We have seen a recent shift to more monthly members, in large part due to the increase in the number of members enrolling through our embedded product channel in which our members enroll on a monthly basis. We also have seen an increase in the number of LifeLock Ultimate members as a percentage of our gross new members.
Customer retention. Our ability to maintain our current member retention rate may be affected by a number of factors, including the effectiveness of our services, the performance of our member services organization, external media coverage of identity theft, the continued evolution of our service offerings, the competitive environment, the effectiveness of our media spend, the timing of employee benefit and breach service enrollments, and other developments.
Our enterprise business relies on the retention of enterprise customers to maintain the effectiveness of our services because our enterprise customers typically provide us with their customer transaction data as part of our service. Losing a significant number of these customers would reduce the breadth and effectiveness of our services. In addition, we believe approximately 13% of the revenue of ID Analytics for the three-month period ended March 31, 2014, or less than 1% of our overall revenue for such period, was derived from direct competitors to our consumer business. As we have given notice of non-renewal to competitors in our consumer business, we have allowed such contracts to lapse, and accordingly, this percentage may decline over time.
Investments to grow our business. We will continue to invest to grow our business. Investments in the development and marketing of new services and the continued enhancement of our existing services will increase our operating expenses in the near term and thus may negatively impact our operating results in the short term, although we anticipate that these investments will grow and improve our business over the long term.
Regulatory developments. Our business is subject to regulation by federal, state, local, and foreign authorities. Any changes to the existing applicable laws, regulations, or rules; any determination that other laws, regulations, or rules are applicable to us; or any determination that we have violated any of these laws, regulations, or rules could adversely impact our operating results. In addition, as previously disclosed, on January 17, 2014, we met with FTC Staff, at our request, to discuss issues regarding allegations that have been asserted in a whistleblower claim against us relating to our compliance with the FTC Order. On March 13, 2014, we received a request from the FTC for documents and information related to our compliance with the FTC Order. A determination that we are in violation of the FTC Order could result in liability for fines, damages, or other penalties or require us to make changes to our services
20
and business practices, and cause us to lose customers, any of which could have a material adverse impact on our business, operating results, financial condition, and prospects. We also collect and remit sales tax in several states related to the sale of our consumer services. Other states or one or more countries or other jurisdictions may seek to impose sales or other tax collection obligations on us in the future. A successful assertion by any state, country, or other jurisdiction that we should be collecting sales or other taxes on the sale of our services could, among other things, increase the cost of our services, create significant administrative burdens for us, result in substantial tax liabilities, discourage current members and other consumers from purchasing our services, or otherwise substantially harm our business and operating results.
For additional factors and risks facing our business see “Risk Factors”.
Basis of Presentation and Key Components of Our Results of Operations
Following our acquisition of ID Analytics in the first quarter of 2012, we began operating our business and reviewing and assessing our operating performance using two reportable segments: our consumer segment and our enterprise segment. We review and assess our operating performance using segment revenue, income (loss) from operations, and total assets. These performance measures include the allocation of operating expenses to our reportable segments based on management’s specific identification of costs associated to those segments.
Revenue
We derive revenue in our consumer segment primarily from fees paid by our members for identity theft protection services offered on a subscription basis. Our members subscribe to our consumer services on a monthly or annual, automatically renewing basis and pay us the full subscription fee at the beginning of each subscription period, in most cases by authorizing us to directly charge their credit or debit cards. In some cases, we offer members a free trial period, which is typically 30 days. Our members may cancel their membership with us at any time without penalty and, when they do, we issue a refund for the unused portion of the canceled membership. We recognize revenue for member subscriptions ratably on a daily basis from the latter of cash receipt, activation of a member’s account, or expiration of free trial periods to the end of the subscription period.
We also provide consumer services for which the primary customer is an enterprise purchasing identity theft protection services on behalf of its employees or customers. In such cases, we defer revenue for each member until the member’s account has been activated. We then recognize revenue ratably on a daily basis over the term of the subscription period.
We derive revenue in our enterprise segment from fees paid by our enterprise customers for fraud and risk solutions, which we provide under multi-year contracts, many of which renew automatically. Our enterprise customers pay us based on their monthly volume of transactions with us, and approximately30% of them are committed to paying monthly minimum fees. We recognize revenue based on a negotiated fee per transaction. Transaction fees in excess of any of the monthly minimum fees are billed and recorded as revenue in addition to the monthly minimum fees. In some instances, we receive up-front non-refundable payments against which the monthly minimum fees are applied. The up-front non-refundable payments are recorded as deferred revenue and recognized as revenue monthly over the usage period. If an enterprise customer does not meet its monthly minimum fee, we bill the negotiated monthly minimum fee and recognize revenue for that amount. We derive a small portion of our enterprise revenue from special projects in which we are engaged to deliver a report at the end of the analysis, which we record upon delivery and acceptance of the report.
Cost of Services
Cost of services in our consumer segment consists primarily of costs associated with our member services organization and fulfillment partners. Our member support operations include wages and benefits for personnel performing these functions and facility costs directly associated with our sales and service delivery functions. We also pay fees to third-party service providers related to the fulfillment of our consumer services, including the premiums associated with the identity theft insurance that we provide to our members, and merchant credit card fees.
Cost of services in our enterprise segment includes the costs related to data analytics and data management, primarily consisting of wages and benefits of personnel and facility costs directly associated with the data analytics and data management.
We expect our cost of services to increase if we continue to increase the number of our members and enterprise customers. Our cost of services is heavily affected by prevailing salary levels, which affect our internal direct costs and fees paid to third-party service providers. Increases in the market rate for wages would increase our cost of services.
21
Gross Margin
Gross profit as a percentage of total revenue, or gross margin, has been and will continue to be affected by a variety of factors. Increases in personnel and facility costs directly associated with the provision of our services can negatively affect our gross margin, as can higher fulfillment costs due to enhancements in our services or the introduction of new services, such as the addition of insurance coverage in our consumer services. A significant increase in the number of members we enroll through our strategic partner distribution channels can also negatively affect our gross margin because we offer wholesale pricing to our strategic partners. In prior periods, our gross margin has also been negatively impacted by sales taxes we paid on behalf of our members and settlements with state tax authorities. Conversely, operating efficiencies in our member services organization can improve our gross margin. We expect that our gross margin may fluctuate from period to period depending on all of these factors.
Sales and Marketing
Sales and marketing expenses consist primarily of direct response advertising and online search costs, commissions paid on a per-member basis to our online affiliates and on a percentage of revenue basis to our co-marketing partners, and wages and benefits for sales and marketing personnel. Direct response marketing costs include television, radio, and print advertisements as well as costs to create and produce these advertisements. Online search costs consist primarily of pay-per-click payments to search engines and other online advertising media, such as banner ads. Advertising costs are expensed as incurred and historically have occurred unevenly across periods. Our sales and marketing expenses also include payments related to our sponsorship, and promotional. In order to continue to grow our business and the awareness of our services, we plan to continue to commit substantial resources to our sales and marketing efforts. As a result, we expect our sales and marketing expenses will continue to increase in absolute dollars for the foreseeable future and vary as a percentage of revenue depending on the timing of those expenses.
Technology and Development
Technology and development expenses consist primarily of personnel costs incurred in product development, maintenance and testing of our websites, enhancing our existing services and developing new services, internal information systems and infrastructure, data privacy and security systems, third-party development, and other internal-use software systems. Our development costs are primarily incurred in the United States and directed at enhancing our existing service offerings and developing new service offerings. In order to continue to grow our business and enhance our services, we plan to continue to commit resources to technology and development. In addition, ID Analytics has historically spent a higher portion of its revenue on technology and development. As a result, we expect our technology and development expenses will continue to increase in absolute dollars for the foreseeable future.
General and Administrative
General and administrative expenses consist primarily of personnel costs, professional fees, and facility-related expenses associated with our executive, finance, human resources, legal, and governmental affairs organizations. Our professional fees principally consist of outside legal, auditing, accounting, and other consulting fees. Legal costs included within our general and administrative expenses also include costs incurred to litigate and settle various legal matters. We expect our general and administrative expenses will increase in absolute dollars for the foreseeable future as we hire additional personnel and expand our office facilities to support our overall growth and incur additional costs associated with our public company and regulatory compliance.
Amortization of Acquired Intangible Assets
Amortization of acquired intangible assets is the amortization expense associated with core technology, customer relationships, and trade names and trademarks resulting from business acquisitions. As of March 31, 2014, we had $45.0 million in intangible assets, net of amortization, as a result of our acquisitions of ID Analytics and Lemon. The intangible assets have useful lives of between one and ten years and we expect to recognize approximately $8.9 million of amortization expense in the year ending December 31, 2014.
Provision for Income Taxes
We are subject to federal income tax as well as state income tax in various states in which we conduct business. Our effective tax rate for the three-month period ended March 31, 2014 approximates the U.S. federal statutory tax rate plus the impact of state taxes and permanent and other temporary differences. For the three-month period ended March 31, 2013, our effective tax rate differed from the statutory rate primarily as a result of our valuation allowance on our deferred taxes, state taxes, and non-deductible expenses.
22
Results of Operations
Comparison of the Three-Month Periods Ended March 31, 2014 and 2013
Total Revenue
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Consumer revenue |
$ |
100,995 |
|
|
$ |
75,094 |
|
|
|
34.5 |
% |
Enterprise revenue |
|
6,591 |
|
|
|
7,001 |
|
|
|
-5.9 |
% |
Total revenue |
|
107,586 |
|
|
|
82,095 |
|
|
|
|
|
Consumer revenue for the three-month period ended March 31, 2014 was $101.0 million, an increase of $25.9 million, or 34.5%, over consumer revenue for the three-month period ended March 31, 2013. The increase in our consumer revenue related primarily to an increase in the number of our members, which grew from 2.6 million as of March 31, 2013 to 3.2 million as of March 31, 2014, an increase of 22%. In addition, our monthly average revenue per member increased 10% to $10.81 for the three-month period ended March 31, 2014 from $9.80 for the three-month period ended March 31, 2013. The increase in members and monthly average revenue per member resulted from the continued success of our LifeLock Ultimate service offering and our advertising and marketing campaigns designed to increase the overall awareness of our services and identity theft.
Enterprise revenue for the three-month period ended March 31, 2014 was $6.6 million, a decrease of $0.4 million, or 5.9%, over enterprise revenue for the three-month period ended March 31, 2013. Enterprise revenue decreased due to a reduction in revenue from enterprise customers who compete with our consumer business as those contracts have been allowed to lapse. In addition, we saw a decrease in transactions from certain end customers due to a slowdown in their business.
Cost of Services and Gross Profit
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Cost of services |
$ |
30,067 |
|
|
$ |
23,804 |
|
|
|
26.3 |
% |
Percentage of revenue |
|
27.9 |
% |
|
|
29.0 |
% |
|
|
|
|
Gross profit |
|
77,519 |
|
|
|
58,291 |
|
|
|
33.0 |
% |
Percentage of revenue |
|
72.1 |
% |
|
|
71.0 |
% |
|
|
|
|
Gross profit for the three-month period ended March 31, 2014 was $77.5 million, or 72.1% of revenue, an increase of $19.2 million, or 33.0%, over gross profit of $58.3 million, or 71.0% of revenue, for the three-month period ended March 31, 2013. The increase in our gross profit resulted primarily from increased revenue associated with the growth in the number of our members and increased monthly average revenue per member. The increase in our gross margin resulted primarily from efficiencies in our member services organization and scalability within certain third party fulfillment contracts as our member base continued to grow.
Sales and Marketing
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Sales and marketing |
$ |
56,847 |
|
|
$ |
41,793 |
|
|
|
36.0 |
% |
Percentage of revenue |
|
52.8 |
% |
|
|
50.9 |
% |
|
|
|
|
Sales and marketing expenses for the three-month period ended March 31, 2014 were $56.8 million, or 52.8% of revenue, compared with $41.8 million, or 50.9% of revenue, for the three-month period ended March 31, 2013. The increase in our sales and marketing expenses resulted from increases in our advertising expenses and external sales commissions. The increase in our sales and marketing expenses reflected our investment to drive new membership growth, our continued advertising of our LifeLock Ultimate service, and our efforts to highlight the growing identity theft issue and to educate consumers.
23
Technology and Development
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Technology and development |
$ |
13,148 |
|
|
$ |
9,024 |
|
|
|
45.7 |
% |
Percentage of revenue |
|
12.2 |
% |
|
|
11.0 |
% |
|
|
|
|
Technology and development expenses for the three-month period ended March 31, 2014 were $13.2 million, or 12.2% of revenue, compared with $9.0 million, or 11.0% of revenue, for the three-month period ended March 31, 2013. The increase in our technology and development expenses resulted primarily from increases in our personnel costs, as we continue to invest in the talent within the organization.
General and Administrative
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
General and administrative |
$ |
13,972 |
|
|
$ |
9,424 |
|
|
|
48.3 |
% |
Percentage of revenue |
|
13.0 |
% |
|
|
11.5 |
% |
|
|
|
|
General and administrative expenses for the three-month period ended March 31, 2014 were $14.0 million, or 13.0% of revenue, compared with $9.4 million, or 11.5% of revenue, for the three-month period ended March 31, 2013. The increase in general and administrative expenses resulted primarily from additional costs associated with our public company compliance, our regulatory compliance, acquisition integration and related intellectual property audits, the expansion of our office facilities, and additional personnel costs, primarily non-cash share-based compensation.
Amortization of Acquired Intangible Assets
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Amortization of acquired intangible assets |
$ |
2,231 |
|
|
$ |
1,966 |
|
|
|
13.5 |
% |
Percentage of revenue |
|
2.1 |
% |
|
|
2.4 |
% |
|
|
|
|
Amortization of acquired intangible assets was $2.2 million for the three-month period ended March 31, 2014, an increase of $0.3 million from the three-month period ended March 31, 2013, and resulted from our amortization of the intangible assets acquired in our acquisition of Lemon in December 2013.
Other Income (Expense)
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Interest expense |
$ |
(87 |
) |
|
$ |
(67 |
) |
|
|
29.9 |
% |
Interest income |
|
60 |
|
|
|
20 |
|
|
|
200.0 |
% |
Other |
|
(11 |
) |
|
|
(4 |
) |
|
|
175.0 |
% |
|
$ |
(38 |
) |
|
$ |
(51 |
) |
|
|
-25.5 |
% |
Other expense for the three-month period ended March 31, 2014 was less than $0.1 million compared with other income of $0.1 million for the three-month period ended March 31, 2013.
24
Income Tax (Benefit) Expense
|
For the Three Months Ended March 31, |
|
|||||||||
|
2014 |
|
|
2013 |
|
|
% Change |
|
|||
|
(in thousands) |
|
|
|
|
|
|||||
Income tax (benefit) expense |
$ |
(3,548 |
) |
|
$ |
150 |
|
|
|
-2465.3 |
% |
Effective tax rate |
|
40.9 |
% |
|
|
-3.8 |
% |
|
|
|
|
Income tax benefit for the three-month period ended March 31, 2014 was $3.5 million compared with an income tax expense of $0.2 million for the three-month period ended March 31, 2013. In the fourth quarter of 2013, in consideration of all available positive and negative evidence, including our historical operating results, current financial condition, and potential future taxable income, we released substantially all of our valuation allowance on our deferred tax assets. As such, for the three-month period ended March 31, 2014, our effective tax rate approximated the U.S. federal statutory tax rate plus the impact of state taxes.
Liquidity and Capital Resources
As of March 31, 2014, we had $143.7 million in cash and cash equivalents, which consisted of cash, money market funds, and open commercial paper, and $47.5 million in marketable securities, which consisted of corporate bonds, municipal bonds, and certificates of deposit. We classify our marketable securities as short-term regardless of contractual maturity based on our ability to liquidate such investments for use in current operations. Additionally, we have an $85 million revolving line of credit, although we have made no draws on the line of credit to date. As of March 31, 2014, we had no outstanding debt. We believe that our existing cash and cash equivalents and marketable securities together with cash generated from operations will be sufficient to fund our operations for at least the next 12 months.
Operating Activities
For the three-month period ended March 31, 2014, operating activities generated $18.3 million in cash as a result of a net loss of $5.2 million, adjusted by non-cash items such as depreciation and amortization of $3.9 million, share-based compensation of $5.5 million, and a deferred income tax benefit of $3.6 million. An increase in deferred revenue related to the overall growth of our business provided operating cash of $17.2 million and we had a decrease in operating cash as a result of changes in other operating assets and liabilities of $0.2 million.
For the three-month period ended March 31, 2013, operating activities generated $12.8 million in cash as a result of a net loss of $4.1 million, adjusted by non-cash items such as depreciation and amortization of $3.1 million and share-based compensation of $2.7 million. An increase in deferred revenue related to the overall growth of our business provided operating cash of $12.5 million and we had a decrease in operating cash as a result of changes in other operating assets and liabilities of $1.4 million.
Investing Activities
For the three-month period ended March 31, 2014, we used $3.9 million of cash to acquire property and equipment and net proceeds from the sales and purchases of marketable securities provided $1.1 million of cash.
For the three-month period ended March 31, 2013, we used $1.3 million of cash to acquire property and equipment.
Financing Activities
For the three-month period ended March 31, 2014, our financing activities generated net cash of $4.3 million as a result of cash received from the exercise of stock options of $4.4 million, offset by $0.1 million paid for employee withholding tax related to net distributions of restricted stock units.
For the three-month period ended March 31, 2013, we used $0.4 million related to the payments of debt issuance costs associated with the refinancing of our credit agreement.
25
Debt Obligations
Credit Agreement
On January 9, 2013, we refinanced our existing credit agreement and entered into a new credit agreement, or the Credit Agreement, with Bank of America, N.A. as administrative agent, swing line lender and issuer of letters of credit, Silicon Valley Bank as syndication agent, Merrill Lynch, Pierce, Fenner & Smith Incorporated as sole lead arranger and sole book manager, and the lenders from time to time party thereto. We refer to the Credit Agreement and related documents as the Senior Credit Facility.
The Senior Credit Facility provides for an $85.0 million revolving line of credit, which we can increase to $110.0 million subject to the conditions set forth in the Credit Agreement. The revolving line of credit also includes a letter of credit subfacility of $10.0 million and a swing line loan subfacility of $5.0 million. The Senior Credit Facility has a maturity date of January 9, 2018. As of March 31, 2014, we had no debt outstanding under our Senior Credit Facility. For the three-month periods ended March 31, 2014 and 2013, we paid an unused commitment fee of less than $0.1 million, which is included in interest expense in the condensed consolidated statements of operations.
Borrowings under the Senior Credit Facility bear interest at a per annum rate equal to, at our option, either (a) a base rate equal to the highest of (i) the Federal Funds Rate plus 0.50%, (ii) the rate of interest in effect for such day as publicly announced from time to time by Bank of America as its “prime rate,” and (iii) the eurodollar rate for base rate loans plus 1.00%, plus an applicable rate ranging from 0.50% to 1.25%, or (b) the eurodollar rate for eurodollar rate loans plus an applicable rate ranging from 1.50% to 2.25%. The initial applicable rate is 0.50% for base rate loans and 1.50% for eurodollar rate loans, subject to adjustment from time to time based upon our achievement of a specified consolidated leverage ratio.
In addition to paying interest on the outstanding principal under the Senior Credit Facility, we are also required to pay a commitment fee to the administrative agent at a rate per annum equal to the product of (a) an applicable rate ranging from 0.25% to 0.50% multiplied by (b) the actual daily amount by which the aggregate revolving commitments exceed the sum of (1) the outstanding amount of revolving borrowings, and (2) the outstanding amount of letter of credit obligations. The initial applicable rate is 0.25%, subject to adjustment from time to time based upon our achievement of a specified consolidated leverage ratio.
We also will pay a letter of credit fee to the administrative agent for the account of each lender in accordance with its applicable percentage of a letter of credit for each letter of credit, which fee will be equal to the applicable rate then in effect, multiplied by the daily maximum amount available to be drawn under the letter of credit. The initial applicable rate for the letter of credit is 1.50%, subject to adjustment from time to time based upon our achievement of a specified consolidated leverage ratio.
We have the right to prepay our borrowings under the Senior Credit Facility from time to time in whole or in part, without premium or penalty, subject to the procedures set forth in the Senior Credit Facility.
All of our obligations under the Senior Credit Facility are unconditionally and jointly and severally guaranteed by each of our existing and future, direct or indirect, domestic subsidiaries, subject to certain exceptions. In addition, all of our obligations under the Senior Credit Facility, and the guarantees of those obligations, are secured, subject to permitted liens and certain other exceptions, by a first-priority lien on our and our subsidiaries’ tangible and intangible personal property, including a pledge of all of the capital stock of our subsidiaries.
The Senior Credit Facility requires us to maintain certain financial covenants. In addition, the Senior Credit Facility requires us to maintain all material proprietary databases and software with a third-party escrow agent in accordance with an escrow agreement that we reaffirmed in connection with the Senior Credit Facility. The Senior Credit Facility also contains certain affirmative and negative covenants limiting, among other things, additional liens and indebtedness, investments and distributions, mergers and acquisitions, liquidations, dissolutions, sales of assets, prepayments and modification of debt instruments, transactions with affiliates, and other matters customarily restricted in such agreements. The Senior Credit Facility also contains customary events of default, including payment defaults, breaches of representations and warranties, covenant defaults, cross defaults to other contractual agreements, events of bankruptcy and insolvency, and a change of control. As of March 31, 2014, we were in compliance with all covenants.
As of March 31, 2014, we had an outstanding letter of credit issued in connection with the revolving line of credit in our Senior Credit Facility in the total amount of $0.1 million.
Off-Balance Sheet Arrangements
We do not engage in any off-balance sheet financing activities, nor do we have any interest in entities referred to as variable interest entities.
26
Contractual Obligations
There were no material changes in our commitments under contractual obligations to those disclosed in our Annual Report on Form 10-K for the fiscal year ended December 31, 2013.
Critical Accounting Policies
Our condensed consolidated financial statements are prepared in accordance with accounting principles generally accepted in the United States of America. The preparation of these consolidated financial statements requires us to make estimates and assumptions that affect the reported amounts of assets, liabilities, revenue, costs and expenses, and related disclosures. These estimates form the basis for judgments we make about the carrying values of our assets and liabilities, which are not readily apparent from other sources. We base our estimates and judgments on historical experience and on various other assumptions that we believe are reasonable under the circumstances. On an ongoing basis, we evaluate our estimates and assumptions. Our actual results may differ from these estimates under different assumptions or conditions.
We believe that the assumptions and estimates associated with revenue recognition for payments and other fees, income taxes, and share-based compensation have the greatest potential impact on our condensed consolidated financial statements. Therefore, we consider these to be our critical accounting policies and estimates.
There have been no material changes to our critical accounting policies and estimates as compared to the critical accounting policies and estimates described in the our Annual Report on Form 10-K for the fiscal year ended December 31, 2013.
Item 3. Quantitative and Qualitative Disclosures About Market Risk.
There have been no material changes in our primary market risk exposures or how those exposures are managed from the information disclosed in Part II, Item 7A of our Annual Report on Form 10-K for the fiscal year ended December 31, 2013. For further discussion of quantitative and qualitative disclosures about market risk, reference is made to our Annual Report on Form 10-K for the fiscal year ended December 31, 2013.
Item 4. Controls and Procedures.
Evaluation of Disclosure Controls and Procedures
Our management, with the participation of our Chief Executive Officer and Chief Financial Officer, has evaluated the effectiveness of our disclosure controls and procedures (as defined in Rules 13a- 15(e) and 15d- 15(e) under the Exchange Act), as of the end of the period covered by this Quarterly Report on Form 10-Q. Based on such evaluation, our Chief Executive Officer and Chief Financial Officer have concluded that our disclosure controls and procedures were effective at the reasonable assurance level as of March 31, 2014.
Changes in Internal Control Over Financial Reporting
There were no changes in our internal control over financial reporting identified in management’s evaluation pursuant to Rules 13a-15(d) or 15d-15(d) of the Exchange Act during the period covered by this Quarterly Report on Form 10-Q that materially affected, or are reasonably likely to materially affect, our internal control over financial reporting.
Limitations on Effectiveness of Controls and Procedures
Our management, including our Chief Executive Officer and Chief Financial Officer, does not expect that our disclosure controls and procedures or our internal controls over financial reporting will prevent all error and all fraud. A control system, no matter how well conceived and operated, can provide only reasonable, not absolute, assurance that the objectives of the control system are met. Further, the design of a control system must reflect the fact that there are resource constraints, and the benefits of controls must be considered relative to their costs. Because of the inherent limitations in all control systems, no evaluation of controls can provide absolute assurance that all control issues, misstatements, errors, and instances of fraud, if any, within our company have been or will be prevented or detected. These inherent limitations include the realities that judgments in decision-making can be faulty and that breakdowns can occur because of simple error or mistake. Controls also can be circumvented by the individual acts of some persons, by collusion of two or more people, or by management override of the controls. The design of any system of controls is based in part on certain assumptions about the likelihood of future events, and there can be no assurance that any design will succeed in achieving its stated goals under all potential future conditions. Projections of any evaluation of controls effectiveness to future periods are subject to risks. Over time, internal controls may become inadequate as a result of changes in conditions, or through the deterioration of the degree of compliance with policies or procedures.
27
For a description of our material legal proceedings, see Note 10 —“Contingencies” in the Notes to the condensed consolidated financial statements included elsewhere in this Quarterly Report on Form 10-Q.
Investing in our common stock involves a high degree of risk. Before deciding to invest in our common stock, you should carefully consider each of the risk factors described in “Part I – Item 1A. Risk Factors” in our Annual Report on Form 10-K for the fiscal year ended December 31, 2013 and all information set forth in this Quarterly Report on Form 10-Q. Those risks and the risks described in this Quarterly Report on Form 10-Q, including in the section entitled “Management’s Discussion and Analysis of Financial Condition and Results of Operations”, could materially harm our business, financial condition, operating results, cash flow, and prospects. If that occurs, the trading price of our common stock could decline, and you may lose all or part of your investment.
There have been no material changes to the Risk Factors described under “Part I – Item 1A. Risk Factors” in our Annual Report on Form 10-K for the fiscal year ended December 31, 2013.
28
10.11A** |
Technology Services Agreement, dated as of January 16, 2014, by and between LifeLock, Inc. and CSIdentity Corporation |
|
|
31.1 |
Certification of Principal Executive Officer required by Rule 13a-14(a) or 15d-14(a) of the Securities Exchange Act of 1934, as adopted pursuant to Section 302 of the Sarbanes-Oxley Act of 2002 |
|
|
31.2 |
Certification of Principal Financial Officer required by Rule 13a-14(a) or 15d-14(a) of the Securities Exchange Act of 1934, as adopted pursuant to Section 302 of the Sarbanes-Oxley Act of 2002 |
|
|
32.1 |
Certification of Chief Executive Officer pursuant to 18 U.S.C. Section 1350, as adopted pursuant to Section 906 of the Sarbanes-Oxley Act of 2002 |
|
|
32.2 |
Certification of Chief Financial Officer pursuant to 18 U.S.C. Section 1350, as adopted pursuant to Section 906 of the Sarbanes-Oxley Act of 2002 |
|
|
101.INS* |
XBRL Instance Document |
|
|
101.SCH* |
XBRL Taxonomy Extension Schema Document |
|
|
101.CAL* |
XBRL Taxonomy Extension Calculation Linkbase Document |
|
|
101.DEF* |
XBRL Taxonomy Extension Definition Linkbase Document |
|
|
101.LAB* |
XBRL Taxonomy Extension Label Linkbase Document |
|
|
101.PRE* |
XBRL Taxonomy Extension Presentation Linkbase Document |
** | Certain information in this exhibit has been omitted and filed separately with the Securities and Exchange Commission. Confidential treatment has been requested with respect to the omitted portions. |
* | Pursuant to Rule 406T of Regulation S-T, these interactive data files are deemed not filed or part of a registration statement or prospectus for purposes of Sections 11 or 12 of the Securities Act of 1933, as amended, are deemed not filed for purposes of Section 18 of the Exchange Act, and otherwise are not subject to liability under those sections. |
29
Pursuant to the requirements of the Securities Exchange Act of 1934, the registrant has duly caused this report to be signed on its behalf by the undersigned thereunto duly authorized.
|
|
|
|
|
|
LIFELOCK INC. |
|
|
|
|
|
Date: May 2, 2014 |
|
By: |
/s/ Todd Davis |
|
|
Name: |
Todd Davis |
|
|
Title: |
Chairman and Chief Executive Officer |
|
|
|
(Principal Executive Officer) |
|
|
|
|
Date: May 2, 2014 |
|
By: |
/s/ Chris Power |
|
|
Name: |
Chris Power |
|
|
Title: |
Chief Financial Officer |
|
|
|
(Principal Financial and Accounting Officer) |
30
 Technology Services Agreement
Technology Services Agreement
 = Maximum Uptime and
= Maximum Uptime and  = where the Delivery Method is not available during Scheduled Hours other than for Permitted Downtime. The values for
= where the Delivery Method is not available during Scheduled Hours other than for Permitted Downtime. The values for  and
and  are measured per calendar month.
are measured per calendar month.